Leading our news with a short, heartwarming story.
 A passenger on a 29 April KLM flight from Uganda to Amsterdam experienced, three hours in, heart attack symptoms and extreme pain. The Dutch passenger’s luck was that a group of passengers were medical volunteers with Cura from the World, a Oklahoma-based group returning from a medical mission to Uganda. Dr. TJ Trad, the founder/CEO and an invasive cardiologist, created an aid station for the passenger where his legs could be raised and his vitals monitored with the assistance of a nurse. The lucky part was that the team had most of its equipment aboard, including a 12-lead ECG to confirm his cardiac status, plus five medications used for emergency treatment. He was stabilized, but the interesting part was that Dr. Trad used his personal AliveCor KardiaMobile to monitor the patient for arrhythmia, the later and high emergency stage. Dr. Trad was carrying it because a year earlier, he had experienced his own heart attack that canceled out his last medical mission trip and used it to monitor himself. With the patient under monitoring and medications, the KLM flight did not have to divert to Tunisia and it landed at Amsterdam Schiphol three hours later. At the hospital, the Dutch patient was examined over 12 hours and eventually discharged, as he was not diagnosed with a heart attack, stroke or pulmonary embolism, according to the passenger’s wife speaking with CNN. Dr. Trad was able to catch his connecting flight home. From an aviation perspective, it underscores the need for medical training and an emergency kit for monitoring this type of incident. Hat tip to Dave Albert, MD, founder and chief medical officer of AliveCor.
A passenger on a 29 April KLM flight from Uganda to Amsterdam experienced, three hours in, heart attack symptoms and extreme pain. The Dutch passenger’s luck was that a group of passengers were medical volunteers with Cura from the World, a Oklahoma-based group returning from a medical mission to Uganda. Dr. TJ Trad, the founder/CEO and an invasive cardiologist, created an aid station for the passenger where his legs could be raised and his vitals monitored with the assistance of a nurse. The lucky part was that the team had most of its equipment aboard, including a 12-lead ECG to confirm his cardiac status, plus five medications used for emergency treatment. He was stabilized, but the interesting part was that Dr. Trad used his personal AliveCor KardiaMobile to monitor the patient for arrhythmia, the later and high emergency stage. Dr. Trad was carrying it because a year earlier, he had experienced his own heart attack that canceled out his last medical mission trip and used it to monitor himself. With the patient under monitoring and medications, the KLM flight did not have to divert to Tunisia and it landed at Amsterdam Schiphol three hours later. At the hospital, the Dutch patient was examined over 12 hours and eventually discharged, as he was not diagnosed with a heart attack, stroke or pulmonary embolism, according to the passenger’s wife speaking with CNN. Dr. Trad was able to catch his connecting flight home. From an aviation perspective, it underscores the need for medical training and an emergency kit for monitoring this type of incident. Hat tip to Dave Albert, MD, founder and chief medical officer of AliveCor.
VA now dubbing the rollout of the Oracle Cerner EHR as a ‘wave’ strategy. Dr. Neil Evans, the acting executive program director of VA’s Electronic Health Record Modernization Integration (EHRM) Office elaborated on the ‘wave’ in an interview with GovCIO Media & Research. Each rollout will be clustered in sites that routinely work together and where patients flow for care from one location to another. For instance, the planned 2026 rollout previously announced in December 2024 will be in four Michigan locations: VA Battle Creek Medical Center, VA Detroit Healthcare System, VA Ann Arbor Healthcare System, and VA Saginaw Healthcare System. The nine additional sites in 2026, except for Alaska standing alone, are similarly clustered [TTA 4 April]. The new news? FTA:
- The White House’s proposed discretionary budget for FY 2026 calls for an increase of nearly $2.2 billion in funding for the EHR program as a “top priority effort.”
- The proposed budget also plans to streamline much of the agency’s over 1000 IT systems, which it claims are “decades old” and “duplicative.”
- It pauses procurement of new systems and directs the U.S. Department of Government Efficiency Service (DOGE) to conduct a full review of the agency’s IT systems alongside the VA.
- Other government agencies are going through the same process: National Oceanic and Atmospheric Administration (NOAA), Defense Department (MHS), and the Coast Guard also are modernizing their EHRs. VA is learning from them as well as the private sector, according to Dr. Evans.
The ‘wave’ needs to work. Veterans Affairs Secretary Doug Collins outlined VA plans at two House appropriations hearings last week on the 2026 and 2027 VA budgets. The total for the EHRM is $3.5 billion in FY 2026 (Federal budgets start in October; the total budget has been dubbed the ‘Big Beautiful Budget’) and is needed for additional rollouts in FY 2027. But given the failures at the six existing implementations and the continuing fixes and patches, in a process that seems like it started in 1900 (actually 2018), one can understand the consternation of Veterans Affairs committee member Rep. Greg Murphy (R-NC): “I’m still dumbfounded at the billions and billions and billions of dollars that have been poured into an EHR that should have never been done in the first place. It’s not a system that should be used for the largest healthcare system in the country.” Healthcare Dive
 Fuze Health launches–phase 2 of a merged LetsGetChecked and Truepill ‘arranged marriage’. The merger of the two last October with digital/mail order pharmacy Truepill operating as a subsidiary of at-home diagnostics via testing kits LetsGetChecked was a $525 million deal that we classified as a ‘smush’ when it was announced last August. Both were heavily invested in by Optum and torching through cash. While $525 million was the purchase value in the headline, only $25 million was in cash and the rest of the financing didn’t add up to the total. The Phase 2 of this entity, Fuze Health, now has a third partner, prescription deliverer Alto, and a new name, Fuze Health. No acquisition amount is mentioned for Alto, which has a total funding of $62.4 million through a June 2021 Series B plus equity crowdfunding (March 2024!) and no financing from Optum (Crunchbase). The only Fuze management mentioned in the release are Alicia Boler Davis, Alto’s CEO, and Paul Greenall, Fuze chief development officer. Their website links back to the four individual companies.
Fuze Health launches–phase 2 of a merged LetsGetChecked and Truepill ‘arranged marriage’. The merger of the two last October with digital/mail order pharmacy Truepill operating as a subsidiary of at-home diagnostics via testing kits LetsGetChecked was a $525 million deal that we classified as a ‘smush’ when it was announced last August. Both were heavily invested in by Optum and torching through cash. While $525 million was the purchase value in the headline, only $25 million was in cash and the rest of the financing didn’t add up to the total. The Phase 2 of this entity, Fuze Health, now has a third partner, prescription deliverer Alto, and a new name, Fuze Health. No acquisition amount is mentioned for Alto, which has a total funding of $62.4 million through a June 2021 Series B plus equity crowdfunding (March 2024!) and no financing from Optum (Crunchbase). The only Fuze management mentioned in the release are Alicia Boler Davis, Alto’s CEO, and Paul Greenall, Fuze chief development officer. Their website links back to the four individual companies.
In 2022, LetsGetChecked acquired Veritas Genetics, now prominently featured as part of Fuze. Also in 2022, Truepill fell under DEA scrutiny with a ‘show cause’ action after being a fulfillment pharmacy for Cerebral and Done Health in their Schedule II controlled substance violations. This was settled in November 2023 with multiple requirements including continuing heightened compliance (DEA release). Fuze Health promotes itself as “a technology-powered home health screening, genomics and pharmacy services provider committed to transforming patient experiences and enabling its healthcare partners – including care providers, health plans, employers and life sciences companies – to excel in an outcomes-focused system.” No mention of investors or backing, as is typical in these announcements. Now go forth and make money. Hat tip to HIStalk 5/23/25
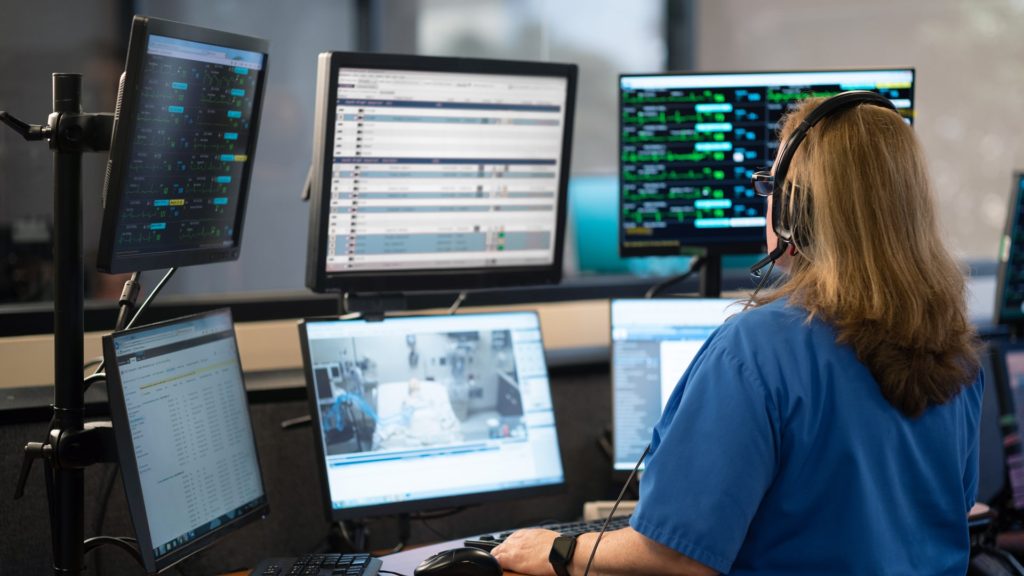
Hacking and ransomware now constitute 92% of healthcare data breaches. Once upon a time, when this Editor reported on what were then unusual data breaches, the more common causes were insider theft, unauthorized access/disclosure, and improper disposal or loss. They have nearly vanished as the ‘business of breaches’ has settled down and internal security has approved. A cross-sectional study published as a research letter in JAMA Network surveyed breaches from 2009 to 2024 using HHS’s Office of Civil Rights (HHS-OCR) reporting. Of 566 incidents in 2024, 457 were “IT incidents” and 61 were tagged as ransomware, totaling 92%. Despite the massive Change Healthcare breach, ransomware breaches fell to 11%. Considering patient records, there were 170 million breached in 2024 and hacking/IT incidents accounted for 91% of the total. Of 732 million records affected from 2010 to 2024, hacking or IT incidents and ransomware (considered as a subset) accounted for 88% (643 million) and 39% (285 million) of incidents. Since 2020, ransomware has affected more than half of all patients annually, reaching 69% in 2024–again, the effect of Change Healthcare. Also Healthcare Dive
















Most Recent Comments